The Resilience Series – The West’s Greatest Vulnerability: Amphibious Critical and Defensive Infrastructure (ACADI)
ABSTRACT
There is a growing realization that to survive and thrive, Western cultures must be resilient against hybrid and unconventional aggression; however, our technological revolution has not only placed us at the forefront of human evolution but also created a fragile dependency, and our greatest vulnerability. This essay, the first in a series on resilience, focuses on Western culture’s greatest dependence: the Internet. The power of the Internet is delivered across sovereign states through what I have termed as Amphibious Critical and Defensive Infrastructure (ACADI), which is vulnerable and not physically designed to withstand kinetic conflict. We pose the question, will a coordinated attack on the West’s ACADI be akin to an ultimate cyber weapon of mass destruction, and what can we do to mitigate such a threat?
Introduction
Global instability has increased over the last decade to a level comparable to that of the Cold War. Russia’s kinetic aggression in Eastern Europe through the attempted invasion and partial occupation of Ukraine has driven a significant change in the deployment of conventional warfare. The threat situation has also dramatically increased from a hybrid warfare perspective, with sabotage and deniable attacks on Western critical infrastructure by Russian foreign intelligence agencies using conduit groups and “Gig” operators, perpetrating attacks on both land and below the sea.
In contrast to the Cold War years, the evolution of the Internet across every level of global society has resulted in the most significant cultural shift since the invention of the wheel or the printing press. Individuals, businesses, and governments are now totally dependent on the Internet to a point where its failure has become too catastrophic to contemplate, but not for all.
Russia and China have shown particular interest in Western online dependency and the vulnerability of ACADI assets. Acutely aware of such global dependencies, Russia is actively planning its own strategic and defensive independence from the World Wide Web. Could this be an indicator of future aggressive intent?
The Asset
Despite what is portrayed, the World Wide Web does not live in the “clouds”; it travels through cables that span the world’s oceans, connecting towns, cities, countries, and continents, creating a long and complex global data supply chain. This chain is supported by an extensive infrastructure network that enables high-speed data movement across approximately 900,000 miles of fiber-optic cable. The data that travels through these cables is responsible for the operability of not only Western nations but also almost every country on the planet, meaning that any interruptions to their activity will affect the productivity, governance, and security of sovereign states and entire global regions. In 2023, Tim Stronge of Telegeography calculated that these cables facilitate the movement of $22.4 trillion a day, a figure, according to the IMF, currently greater than the GDP of every national economy in the world apart from the US.
The impressive transmission speeds of fiber-optic cables have revolutionized modern telecommunications and data-driven technology, being considerably faster than satellite communication and enabling the rapid exchange of vast amounts of data globally with minimal signal degradation and latency. This is particularly relevant considering the emergence of AI and cryptocurrencies. Yet despite their importance to Western operability and survival, data supply chains are predominantly and “critically” exposed to, and unprotected from, current and evolving physical threats.
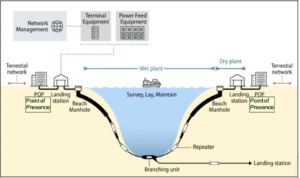
What I like to refer to as the data supply chains consist of amphibious “wet” and “dry” phases as they carry global data between coastal landing stations. The “wet” segment of the submarine cable system, consisting of the cable itself, the repeaters, and the branching units, makes landfall at a beach manhole (BMH), which, in turn, connects to the “dry” segment Transmission Line Amplifier (TLA) as part of the Submarine Line Terminal Equipment (SLTE) and landing station through a short cable and on to the terrestrial networks and data centres.
Submarine Communication Cable System and its components. Source: Congressional Research Service, Undersea Telecommunication Cables: Technology Overview and Issues for Congress.
Fiber optic communication cables have relied on security through obscurity ever since they were first laid on the seabed, suffering a limited number of deniable instances of sabotage from ships dragging anchors and damaging cables, resulting in limited failures.
It is the author’s opinion that Western democracies have, up to now, relied on a fragile hybrid peace to protect their most valuable assets. But what happens to those assets and our dependence on them when peace becomes a memory, and those same assets constitute our greatest weakness?
Evolving threats against Western vulnerability
To understand their relevance in context, the threats to Amphibious Critical and Defensive Infrastructure (ACADI) need to be analyzed within three geopolitical verticals, each requiring separate analysis across the strategic, operational, and tactical levels.
- The peacetime threat situation
- The hybrid conflict threat situation
- The kinetic conflict threat situation
This approach is crucial as it ultimately identifies the levels of protection required to ensure resilience during periods of contrasting geopolitical instability and proactively guards against peacetime mitigation measures being deployed against hybrid or kinetic warfare threats.
Peacetime Threats
Threats to critical infrastructure are defined across two primary vectors: cyber and physical, with the physical vector being further categorized into aggressive and natural threats, as well as the danger posed by structural decay.
All international data, including that of the defined critical infrastructure sectors, is over 95% communicated through vulnerable and remote undersea fiber optic cables and land-based infrastructure. Considering that Russian hybrid warfare doctrine has highlighted the importance of targeting the West’s critical infrastructure, and in particular that which facilitates the Internet, it would be reasonable to think that ensuring its resilience against physical attack and natural threats would be paramount. Assumptions can, of course, be misleading.
Organizations, such as the International Cable Protection Committee (ICPC), report that natural hazards, including earthquakes and underwater landslides, are responsible for only around 10% of the 150-200 cable faults that occur each year. However, when they do occur, such natural processes can damage multiple cable systems simultaneously, sometimes across large areas. The ICPC data supports further open-source intelligence (OSINT), in stating that direct and “accidental” human activity (justified under plausible deniability) is the primary threat to undersea infrastructure during peacetime.
The number of internationally available specialist ships used to lay and repair fiber optic cables, at the time of writing, is believed to be approximately 60; the exact figure is either unknown or not publicly disclosed. Not all of these ships are equipped to both lay and repair damaged cables, however, and at the current rates of reported damage, they are contracted months and sometimes years in advance. Peacetime demand for cable repair ships exceeds supply; currently, the industry appears to be “just” coping, yet many of these ships are ageing. At the time of writing, the UK, for example, lacks sovereign undersea cable repair capability. It takes about three years to build a new cable ship and ten years to train the crew. After a “splurge” of investment around the turn of the century, no new cable ships were delivered globally between 2004 and 2010, and only five were delivered between 2011 and 2020.
From a peacetime perspective, the low frequency of natural disasters and accidental human interference leading to cable failures is costly but operationally insignificant. However, the consequences of a coordinated attack resulting in multiple failures and the subsequent cascading effects have the potential to impact national, regional, and global stability. Our dependence on these amphibious assets cannot be overstated; without them, our modern societies would be unable to operate, our governments would be unable to govern, and we would be unable to defend ourselves effectively from attack. History has shown that “peacetime” complacency leads to an inability to defend against aggression, a Western cultural characteristic that Russia seeks to exploit.
Hybrid Warfare – Situational analysis (Strategic, Operational, Tactical)
Russia’s “multi-type” hybrid conflict architecture is well documented within its New Generation Warfare (NGW) doctrine. NGW is less siloed than the Western approach, prioritizing psychological and people-centered aspects over traditional military concerns. Russian NGW emphasizes a phased approach to non-military influence, such that armed conflict, if it arises, is significantly less costly in human or economic terms for the aggressor than it would otherwise be. It was first enunciated in 2013 by General Valery Gerasimov, Chief of the General Staff of the Russian Armed Forces, First Deputy Minister of Defense.
In 2007, Frank Hoffman wrote that “simultaneous use of multiple types of warfare” refers to a complex combination of conventional and unconventional or hybrid warfare. Such a combination enables the exploitation of economic, social, religious, cultural, political, legal, racial, commercial, chemical, biological, nuclear, and natural resources, as well as environmental factors, aimed at negatively impacting national stabilization. The ultimate result is to diminish a nation’s ability to govern or defend itself.
Russia is in no doubt that it is in the non-military phase of a hybrid war with the West, yet the West does not believe that it is at war with Russia. The West is still on a peacetime footing, yet supporting countries like Ukraine, which are fighting a kinetic war.
Such a non-military warfare doctrine highlights the identification and manipulation of national dependencies as a formidable weapon; the West’s internet dependency has not gone unnoticed. Russia and China are aware that the destruction of a nation’s online capability through physically attacking its ACADI can be operationally and psychologically decisive.
To make things easier for an aggressor, there are seven significant single points of wet (sub-sea) and dry (land-based) failure along a global data supply chain that threaten the whole system’s operability:
| CADI (Data Supply Chain) Vulnerabilities – Wet Assets | CADI (Data Supply Chain) Vulnerabilities – Dry Assets |
| Cable repeaters | Data Centers |
| Fiber optic cables | Beach manholes |
| Branching Units | Points of presence |
| Landing Stations |
Russia has committed significant assets into monitoring and “stress testing” the resilience of Western ACADI both during and since the Cold War.
Such maritime assets include submarine and surface vessels, both military and civilian registered, and tasked with conducting surveillance, reconnaissance, and in some cases, deniable sabotage operations. Such activities have increased in recent years, with Russia constantly testing the willingness of the West to retaliate.
A formidable hybrid warfare asset is the Russian “Shadow Fleet” of old and poorly maintained vessels that fly under various foreign flags to break Western oil sanctions imposed after the invasion of Ukraine. Usually under opaque ownership and with similar insurance cover, they have a dual role when required. Alongside sanction busting, they aim to disrupt the undersea cables of their adversaries under the cover of plausible deniability when opportunities arise. Research from the Brookings Institution indicates that the shadow fleet has steadily expanded from fewer than 100 vessels in February 2022 to 343 vessels by 2025.
Kinetic War – Threat Situational Analysis (Strategic, Operational, Tactical)
So, what happens when deniability is no longer required? When potential enemies deploy their doctrine and lethal capabilities without restraint?
Indications are that a country targeted by Russia can expect an early physical attack on its ACADI as a precursor to a kinetic attack. The Russian approach of treating the enemy as a multi-level system offers a significant operational insight into how potential adversaries assess the West’s holistic strengths and weaknesses, and how they would best deploy their offensive force concentration.
One of Russia’s most important, effective, and sensitive assets is the Main Directorate of Deep-Sea Research (GUGI), also known as Unit 40056, a classified unit within the Russian Ministry of Defense. It operates from its base in Olenya Guba on the Kola Peninsula of the Barents Sea, home to the 29th Special Purpose Submarine Brigade, which includes small submersibles and carrier submarines like the BS-64 Podmoskovye and BS-136 Orenburg. The fleet also consists of the Belgorod, a special-purpose nuclear submarine capable of carrying Poseidon unmanned underwater vehicles and autonomous deep-sea stations.
The GUGI’s specialist units consist of arguably the most highly trained of Russia’s elite troops, and it is important to note that they have (at the time of writing) not been deployed to Ukraine, despite Russia’s insatiable demand for reinforcements in that theatre. There is no definite OSINT explanation for this; however, a reasonable assumption would be that such a highly specialist forward tactical asset, with training similar to that of Russia’s cosmonauts, would be considered too valuable to be deployed in a conflict of attrition and is therefore being held for future hybrid surveillance and sabotage operations or as the “tip of the spear” in a future kinetic war. To support this theory, OSINT from the RUSI Russian Military Report, via Russian publications, has reported that naval personnel on attachment with GUGI in 2012 were earning 600,000 Rubles ($20,000) a month, linked to the periods spent at extreme depths.
Such highly trained elite units pose operational threats to NATO’s entire ACADI landscape, as they are specifically trained and equipped to not only disrupt but also potentially destroy the internet capability of a significant number of member states at pace. Without a major defensive upgrade to NATO’s ACADI, such tactical aggression would have the potential to dramatically affect the operational and strategic balance of any future battlespace and concurrently the domestic ability of nations to survive to fight.
What are the consequences of ACADI failure?
NATO’s enemies possess the capability and, no doubt, have conducted planning to destroy its greatest dependency, but what does that mean?
Failure of data supply chains is of significant strategic concern to national and alliance (NATO) survivability. The Internet is the vehicle through which the movement of global finances travels, and all countries operate. A benchmark to judge the economic value of the Internet of Things (IoT) is the financial cost of internet failure for just one day.
The national cost of internet failure for 24 hrs.
| Country | The Cost of Internet Failure over 24hrs ($) |
| United States | $11,014,601,859 |
| China | $9,897,063,274 |
| United Kingdom | $3,271,132,526 |
| Japan | $2,714,477,506 |
| Germany | $1,498,942,239 |
| India | $1,431,042,434 |
| South Korea | $1,270,826,722 |
| France | $871,276,534 |
| Italy | $643,251,995 |
| Canada | $576,611,171 |
| Total | $33,189,226,260 |
Source. Slingerland, C (2024). The Cost of Shutting the Internet. CloudZero.
These figures become even more significant when compared against national budgets. The annual UK Defense budget for 2024/25 was approximately £66 billion or $87.7 billion; it would take just 24 days of failed internet connectivity for the sovereign cost to equate to the entire UK Defense budget. From a US perspective, with the world’s largest defense spending, which (according to the FY2026 discretionary defense budget) will exceed USD1 trillion, a 3.2% proportion of GDP by 2026, parity between the financial cost of internet failure losses and the annual defense budget would occur in approximately 91 days or 3 months.
China, with the second-highest global defense spend, with an approximate $247 billion (declared) annual budget (with a recent increase of 7.2%), would take 25-26 days of financial loss from a failed internet capability to match its defense budget. Interestingly, the UK and China would be impacted over a very similar timescale.
Russia is not included in the research of the world’s top twenty countries most impacted by the Internet, or, conversely, those most dependent on the Internet of Things, despite having an internet penetration rate of 90.87%. Russia is developing a home-based sovereign-only web network, as defined by legislation adopted in 2019. The aim is to self-partition Russia from the World Wide Web, thereby reducing its dependence on a globally controlled capability and enabling it to effectively operate its critical infrastructure independently. OSINT has suggested that preparations are rapidly underway.
With Russia independent of the cascading effects of internet loss and immune to like-for-like retaliation attacks, it provides them with a decisive unconventional capability to dominate both the hybrid and conventional battle spaces. They can achieve this by diminishing the West’s critical infrastructure operability, shaping and weakening a target landscape to their advantage, and supporting their drive from a deniable hybrid to a successful kinetic attack. It could be said that destroying an adversary’s ACADI is a 21st-century prerequisite for success in any future war, much the same as dominating the air or destroying conventional logistical supply chains.
What does the West need to do to protect its Amphibious Critical and Defensive Infrastructure and strategic data supply chains?
Strategically. Understanding and accepting threats against a primary dependency is paramount. All threats must be identified, analyzed, and accepted (or not) before responsibility for mitigation can be determined and agreed upon, and any action taken. Accepting a threat and not acting upon it (for budgetary reasons, for example) is irresponsible and potentially catastrophic. To this end, the seabed defense challenge and broader non-military warfare threats require heightened official acceptance and collaboration between the government and the private sector to address them.
In January 2025, NATO Secretary General Mark Rutte announced the deployment of Baltic Sentry, which will involve a range of assets, to support the protection of ACADI. This is a significant first step, which hopefully will evolve in response to accepted threats; however, this cannot happen without the introduction of new funding mechanisms.
The concept of sovereign ACADI Public Private Partnership (PPP) investment vehicles, or an equivalent form of strategic finance, initiated across the NATO member states and their allies, has now become a critical defense requirement. Unlike Russia, the majority of NATO ACADI is privately owned/controlled, yet has a significant relevance to individual sovereigns and the NATO Alliance’s security.
Operationally and tactically. The financing of ACADI resilience and defense is critical, but what does it buy? What is operationally and tactically required to provide a credible deterrent against a coordinated and sustained attack as described in this document?
In a kinetic warfare situation, it is tactically easier and more effective to attack fiber optic and energy cables using undersea area weapons that result in multiple and devastating destruction through blast. The accepted and proven form of defense of a linear asset has been to deploy a layered system of barriers and activities that together form a credible deterrent against physical aggression. From an ACADI perspective, this must include:
- Air asset capabilities,
- Land asset resilience and defense capabilities,
- Surface capability,
- Subsea capability,
- Seabed capability,
- Asset (cable, pipeline, and associated land/sea infrastructure) up-armoring and monitoring capabilities.
- Deployment of an armored independent sovereign internet capability to be used by official and identified critical infrastructure sectors in the event of a significant internet outage.
Deploying layered defense capabilities against a constant threat requires a significant and dedicated military commitment and is by no means foolproof. Physically enhancing supply chain resilience by up-armoring ACADI assets is therefore critical, as it is the only contiguous defensive capability option, providing the last line of defense or the first line of resilience in the layered approach. In addition, NATO member states would also be advised to implement a parallel, armored, and independent internet capability to facilitate resilient, sovereign critical infrastructure and defense connectivity, as Russia has done.
To gain a greater understanding of the threats against Western ACADI and the non-military threat spectrum within which it is located, an in-depth situational analysis must be conducted from which informed and relevant holistic operations can be coordinated. It is recommended that such analysis be conducted in research form at the national and allied levels to ensure continuity strategically, yet independent to ensure national operational and tactical relevance. It is advised that any such doctrine be deployable rather than just debated, and include government, private sector, and civil society input. It is recommended that, in addition to the military, private, and civil sector requirements, three ACADI essential components be included, but not limited to:
1) Physical up-armoring of ACADI
2) The development of an armored sovereign web capability
3) Active social development to meet the challenges of the cascading effects of internet failure or a reduction in capability.
Summery
Amphibious Critical and Defensive Infrastructure (ACADI) supports our entire modern Western culture; without it, we cannot communicate, travel, work, access clean water, purchase essential goods, or effectively defend our freedoms. These assets, which give NATO and the West their military dominance and the protection it affords, are currently protected against peacetime threats. What would be the outcomes in the event of an escalation in hybrid threat levels or a kinetic war? It would undoubtedly provide adversaries the ultimate unconventional advantage: a cyber weapon of mass destruction.
The post The Resilience Series – The West’s Greatest Vulnerability: Amphibious Critical and Defensive Infrastructure (ACADI) appeared first on Small Wars Journal by Arizona State University.
Related Articles
Romantic partner helped lead to deadly capture of top cartel leader
A trusted associate of one of the cartel leader’s romantic partners escorted...
Spain’s conservatives set terms for far-right alliance
Spain’s main conservative People’s Party (PP) has published conditions for a possible...
Russia’s ‘death economy’ and Ukrainian resistance: Four years of war in Ukraine
PRESS REVIEW – Tuesday, February 24, 2026: First, the fourth anniversary of...
Mandelson’s Arrest Adds to Scandal That Has Rattled Starmer and Labour Party
The arrest of the British former envoy to Washington, long a key...








Leave a comment